Since 1975, firmware that interfaces hardware and software is the UEFI and BIOS that boot computers before they can load the operating systems. UEFI upgrades 16-bit BIOS constraints, allowing Secure Boot malware blocks, GPT huge drives, graphical menus to text screens. Contemporary PCs fall out of UEFI; amateur hackers make prudent adjustments to prevent bootloops, upgrade problems that can cost hours.
BIOS Basics: Legacy Boot Firmware
BIOS (Basic input/output System) starts up CPU, RAM, drives one by one through 1MB ROM chip-text menus are used with keyboard arrows. Published 1975, supports 2TB MBR partitions (caps), four primaries (max), booting slow single OS loaders. Unauthorized changes can be prevented using password locks; legacy mode, old Windows XP, DOS floppies. Boot through F2/Del at POST beep- unsafe boot without cooling CPUs.
UEFI Evolution: Modern Firmware Standard
Unified Extensible Firmware Interface executes 32/64-bit, boot files are loaded on ESP FAT32 partition, init slashes boot times are 2-3x less than BIOS chains. GPT tables support 128+ partitions, 9 zettabytes theoretically; mouse-based GUIs are similar to windows applications. Drivers Built-in support GPUs, pre-OS networks; updateable modules through USB flash manufacturers such as ASUS EZ Flash.
Secure Boot Explained: Malware Gatekeeper
On Windows 11, default-enabled, calculates the cryptographic integrity of digital signatures, which can block rootkits infecting 90% of bare-metal attacks by Microsoft, OEM keys only boot trusted loaders. Disabled Linux distros can use unsigned hacks; dual-booters can switch through boot order. Quarterly updates on vulnerabilities have been done- Shima vulnerability bypassed through physical SPI flash dump.
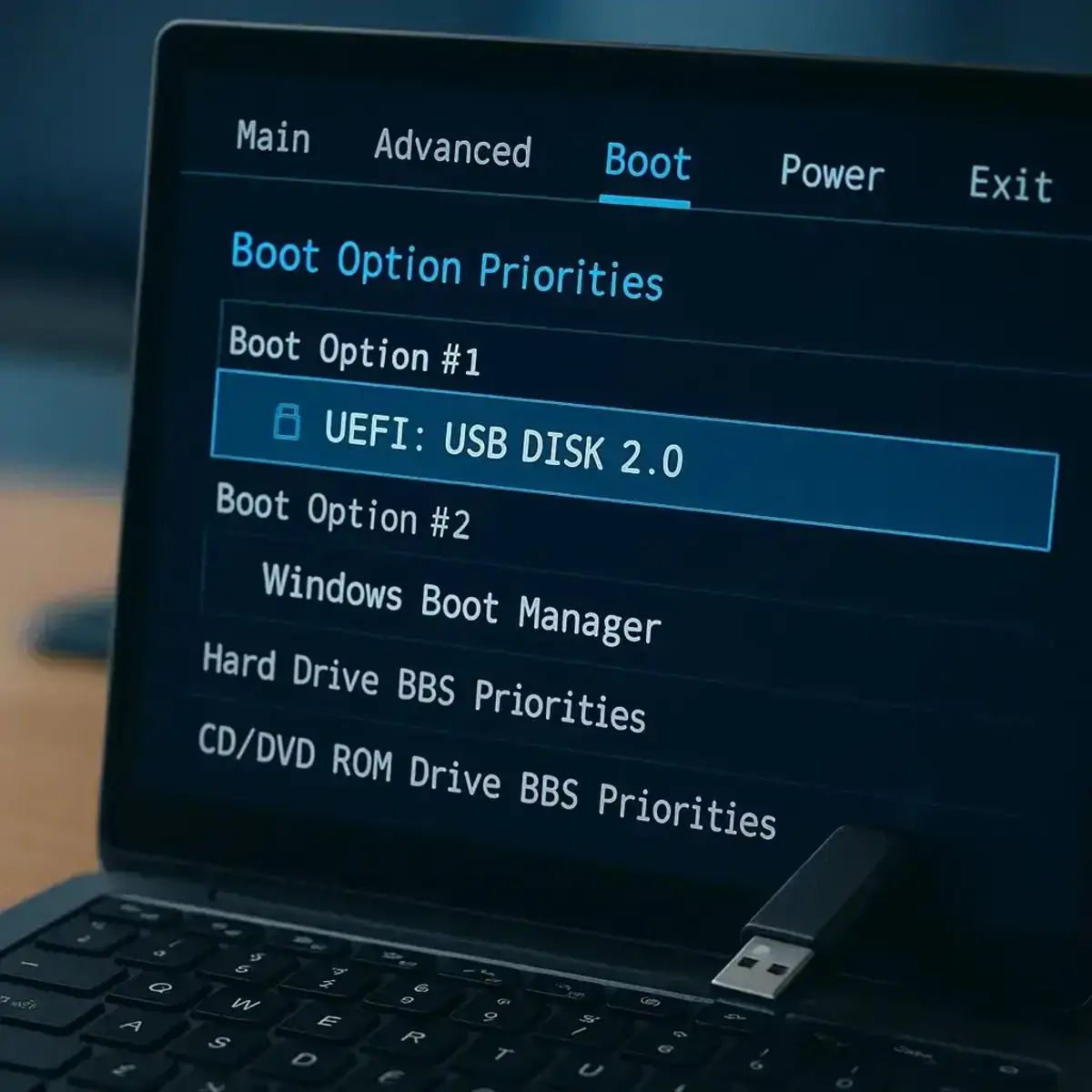
Accessing and Navigating Settings
F2/Del/F10/F12 (motherboard specific) Power-on spam UEFI displays logos, no beeps of BIOS progress bars. There are tabs which are organized as: Main (BIOS/UEFI version, date), Advanced (CPU ratios, XMP RAM), Boot (Secure Boot toggle, CSM legacy), Security (TPM 2.0 fTPM), Save-Exit (F10 saves). Fast Boot bypasses 10 second POSTs on peripherals; reset defaults F9 avoids risk of bricking.
BIOS vs UEFI: Key Differences Table
| Feature | BIOS | UEFI |
|---|---|---|
| Mode | 16-bit real | 64-bit protected |
| UI | Text/keyboard | Graphical/mouse |
| Partition | MBR/2TB/4 max | GPT/9ZB/128 max |
| Boot Speed | Slow sequential | Fast parallel |
| Security | Password only | Secure Boot + TPM |
| Storage | Motherboard chip | ESP .efi files |
Switching Modes and Compatibility
CSM (Compatibility Support Module) of UEFI simulates the old OS- disable to pure UEFI benefits. Windows installers identify auto; Linux GRUB installs EFI stubs. Dual-boot: put NVMe SSDs at the top of the list in Boot Order; above SATA. USB keys with legacy USB keys fail GPT convert to MBR2GPT tool without risks.
Common Tweaks for Performance
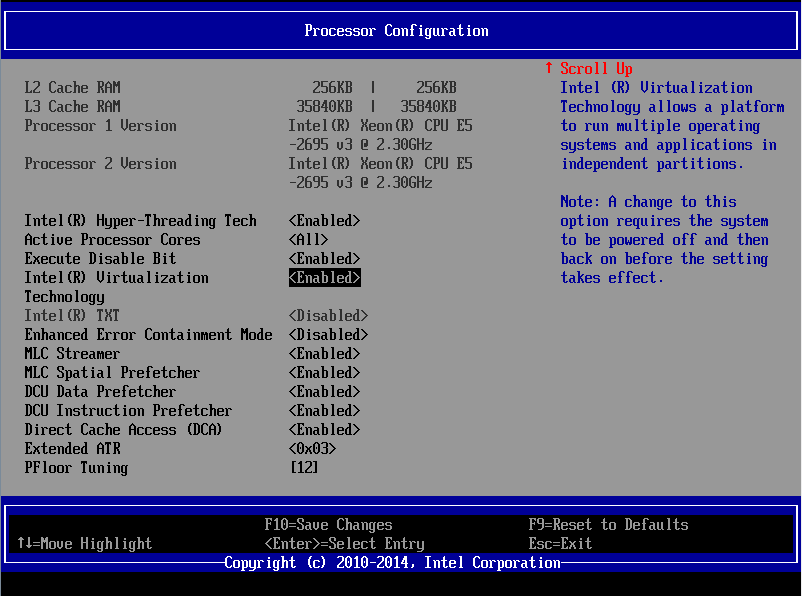
XMP profiles automatically overclock OC RAM to 3200MHz+; C-States save 5% idle power. VT-x/AMD-V virtualization required by VMs; Resizable BAR gains GPUs 10 percent FPS. Secure Boot off supports Hackintosh, custom kernels-re-enable after installation.
Troubleshooting Boot Failures
No POST? Obvious CMOS coin cell/jumpers 5 minutes. Boot loops: fingerprint reader, Secure/CSM, update firmware, USB DOS. Black screens: built-in graphics compel using PCIe configuration. Windows refuses? Match install media mode ( Rufus toggles).
Master menus realize hardware potential BIOS relics are forgotten, UEFI future-proofs hardware. Make small modifications; bricks require motherboard replacements. Downtime disasters are prevented with knowledge.


